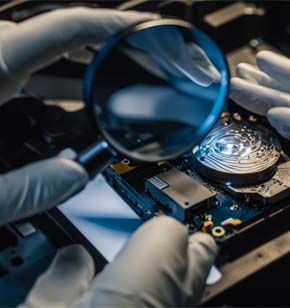
Data Backup, Forensic & Recovery Solutions
We offer data backup, forensic, and recovery solutions to protect and restore your critical data.
Why data backup is the last line of defense
In the event of a catastrophic failure or a successful cyberattack, having a robust backup and protection strategy ensures that you can recover your data with minimal downtime and data loss. This is crucial because:
- Ransomware attacks: If your primary data is encrypted by ransomware, backups allow you to restore your data without paying the ransom.
- Hardware failures: Physical devices can fail unexpectedly, but backups ensure your data isn’t lost permanently.
- Natural disasters: Events like floods or fires can destroy physical data storage, but off-site backups keep your data safe.
- Design
- Installation
- Maintenance
Data backup and recovery serves as the last line of defense against data loss, corruption, and cyber threats. This critical cybersecurity measure ensures that organizations can recover their valuable information even when other security layers fail. Data backup is the process of creating and storing copies of important data in secure locations. It acts as a fail-safe mechanism, allowing for the restoration of lost or corrupted information. As cyber threats become more sophisticated, traditional security measures like firewalls and antivirus software may not always be sufficient to prevent attacks.
What are common cyber threats that can result in data loss?
Common cyber threats that can lead to data loss include:
Malware: Malicious software like viruses, worms, and trojans can corrupt or delete data, and even provide unauthorized access to your systems.
Ransomware: A type of malware that encrypts your data and demands a ransom for the decryption key. This can result in significant data loss if backups are not available.
Phishing attacks: Cybercriminals use deceptive emails or websites to trick individuals into revealing sensitive information, which can then be used to access and steal data.
Social engineering: Manipulating individuals into divulging confidential information, often through impersonation or psychological manipulation.
Weak and stolen credentials: Using weak passwords or having credentials stolen can allow unauthorized access to systems and data.
Backdoor and application vulnerabilities: Exploiting weaknesses in software or systems to gain unauthorized access to data.
Improper configuration and exposure via APIs: Misconfigured systems or exposed APIs can be exploited to access and steal data.
DNS attacks: Manipulating the Domain Name System to redirect traffic to malicious sites, potentially leading to data theft.
Why do I need a last line of defense for my data?
Having a last line of defense for your data is crucial for several reasons:
Unforeseen threats: Despite the best security measures, new and sophisticated cyber threats can still breach defenses. A last line of defense, like backups, ensures you can recover your data even if an attack succeeds.
Human error: Mistakes happen, such as accidental deletions or misconfigurations. A robust backup system can mitigate the impact of these errors.
Hardware failures: Storage devices can fail unexpectedly. Regular backups ensure that your data is not lost due to hardware issues.
Natural disasters: Events like fires, floods, or earthquakes can destroy physical data storage. Offsite backups protect against such scenarios.
Compliance and legal requirements: Many industries have regulations requiring data protection and retention. A last line of defense helps meet these legal obligations.
Business continuity: Ensuring that your business can quickly recover from data loss incidents minimizes downtime and maintains customer trust.
In essence, a last line of defense provides peace of mind, knowing that your data is safe and can be restored in the face of various threats. It’s an essential part of a comprehensive data protection strategy.